If you’ve followed me on twitter for a while you’ve known I’ve been a big fan of Windows Admin Center since it was called Project Honolulu. In this post I’ll show you in depth, why you should replace RDCMan with Windows Admin Center.
For those of you not familiar with Windows Admin Center this is the description from the official page.
Windows Admin Center is a locally deployed, browser-based app for managing Windows servers, clusters, hyper-converged infrastructure, as well as Windows 10 PCs. It comes at no additional cost beyond Windows and is ready to use in production.
Recently there has been much consternation and complaining because RDCMan is depreciated and won’t be patched for a pretty big vulnerability. When Windows Admin Center was recommended as the alternative, it was largely met with scoffs. I was even called “out of touch.” What people are failing to understand is that Windows Admin Center is the tool to use, whether they like it or not.
If you don’t believe me that Windows Admin Center is the current and future tool to use for management of Windows Servers. To quote Jeff Woolsey Principal Program Manager, Azure Stack HCI/Windows Server/Hybrid Cloud.
Time for a little reminder folks… All new GUI investments for Windows Server are in Windows Admin Center. ALL OF THEM. Windows Server 2019 includes brand new capabilities like System Insights, and the awesome Storage Migration Service.
There are features in Windows Server that you cannot do within Windows and the only way to do them is in Windows Admin Center. I would expect that to only increase, not decrease.
Management of Windows Environments
Taking a step back for a moment to talk about broader management of a Windows environment. This includes a number of tools, products or services.
I’ve used RDCMan in several environments. Its a simple RDP management tool. Unless no one has filled me in on the super secret awesome sauce, its a pretty simple and basic tool that only does one thing. Which leads to the problem I have with it, is that all it allows is RDP access. This doesn’t cover things like using the MMC console for, Certificates and other tasks or being able to modify the Registry or view Events and other such tasks. So now I have something like:
- SCCM
- SCVMM/HyperV Manager/Cluster Manager (or all three, le sigh)
- SCOM
- RDCMan
- MMC consoles
- RSAT tools (ADUC, GPO, etc)
and PowerShell to manage servers and environments. That’s a lot of consoles to maintain and manage an environment.
The main reason anyone RDPs into a server is to perform many of the tasks I’ve mentioned above. Server core has been the unofficial officially recommended deployment for Windows Server by Microsoft. Anecdotally from all the environments I’ve been in I’ve never seen a production Server Core deployment.
However, Windows Admin Center allows much easier management of Server Core and it would not surprise me in the least to find out that Server Core installs are increasing with Windows Admin Center adoption. The idea behind Windows Admin Center is to make management easier, for everyone. The main reason hardly anyone adopted server core before WAC is because it was just plain too hard to manage. Your average Sys Admin isn’t using PowerShell every day, and they’re sure not writing scripts to automate or configure servers.
RDCMan and Legacy Tools
As I mentioned above, some are disappointed on the twitterverse because it appears RDCMan is depreciated and won’t be patched. RDCMan was last updated to 2.7 in 2014. Just think about that for a minute. Since 2014 we’ve had two major releases of System Center, 2016 and 2019. SCCM changed to the current branch method and gets updated with major releases 2 or so times a year. Azure switched from the classic management model to Azure Resource Manager. I would hazard that the person(s) that managed RDCMan may not even work at Microsoft anymore, or have long since moved on to bigger and better things within Microsoft.
Conversely, look at the release history of Windows Admin Center.
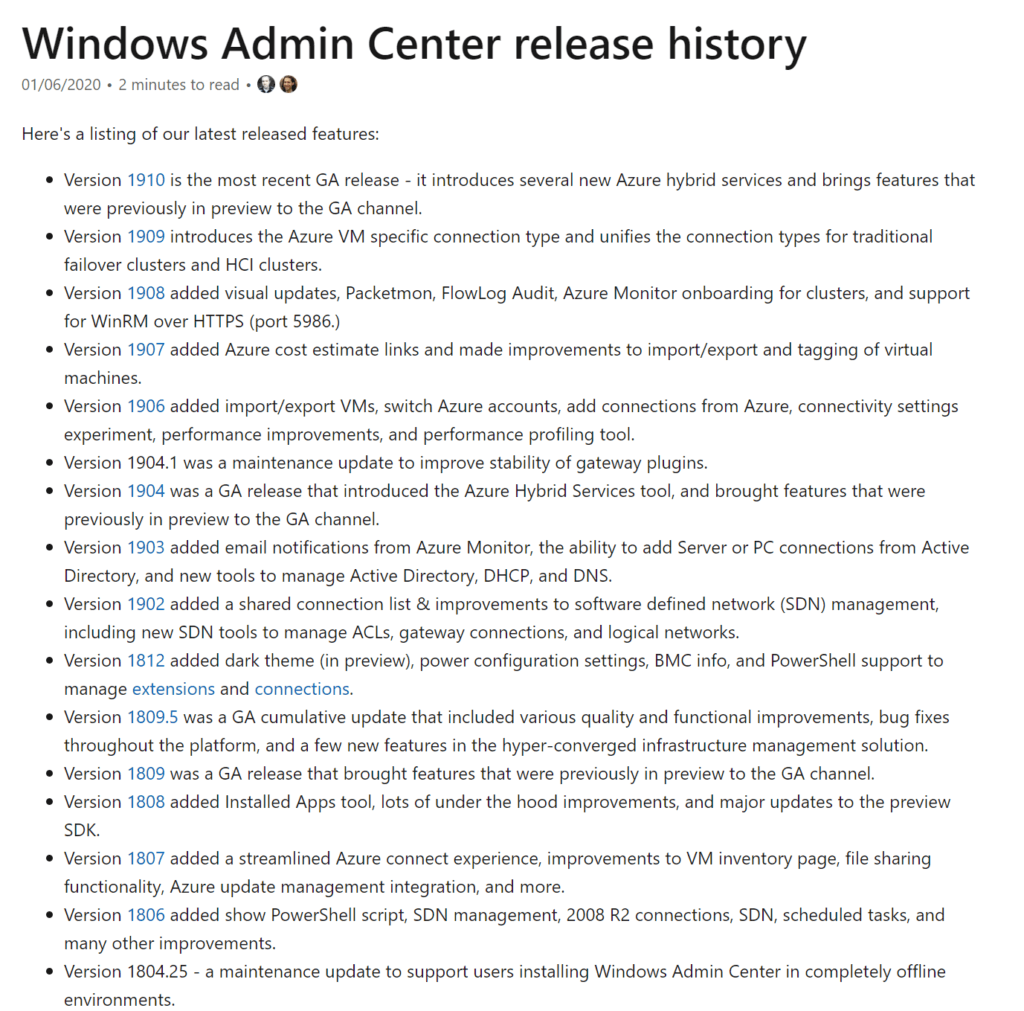
16 releases in less than 2 years. If that doesn’t tell you where the focus is, nothing will. You also have the opportunity to provide feedback. Microsoft absolutely does read the feedback. If Windows Admin Center doesn’t have something that you want or need, tell them.
I get it, I too have gotten attached to a tool and have been crushed when its no longer being updated. I loved, LOVED Orchestrator. This blog was posting about Orchestrator when almost no one else was. The writing was on the wall though. I saw what MVPs were and weren’t posting about, and saw the release notes for Orchestrator 2016. But times changes and sometimes we have to change with them. As much as I loved Orchestrator, I’m now literally writing a series on why and how you should migrate from the tool.
Windows Admin Center
I’m not going to show you how to install it, its stupid simple to install and MS has provided very good instructions. I use it on Server Core running a formerly called Storage Spaces Direct, now called Azure Stack HCI in my lab. However you can install it locally on your laptop, just like RDCMan. You can add the servers you want to connect to just like RDCMan. You can add via Active Directory, CSV or one by one. For this blog I did a brand new install on my laptop just to show how even non domain joined computers can manage Servers in a domain.
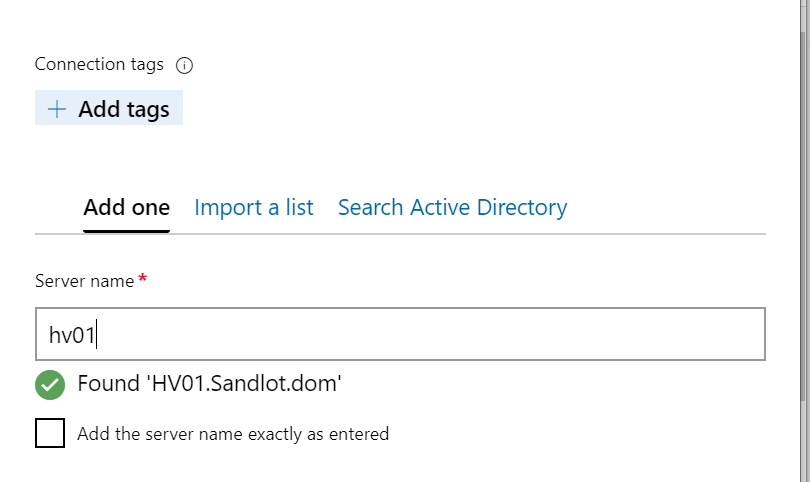
Adding my HyperV host from my laptop. I’d like to point out that my laptop is not joined to my lab domain. In addition to being called out of touch, I was also presumed to have only worked in perfect environments with a single domain. Given that I can add my lab host to my un-trusted laptop, I would imagine enterprising sys admins can figure out how to manage multiple AD domains with Windows Admin Center.
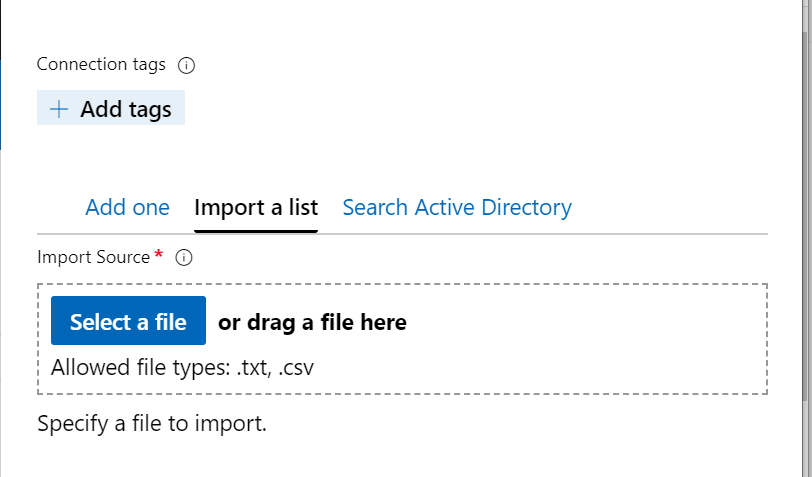
You can also add via CSV or AD as pictured.
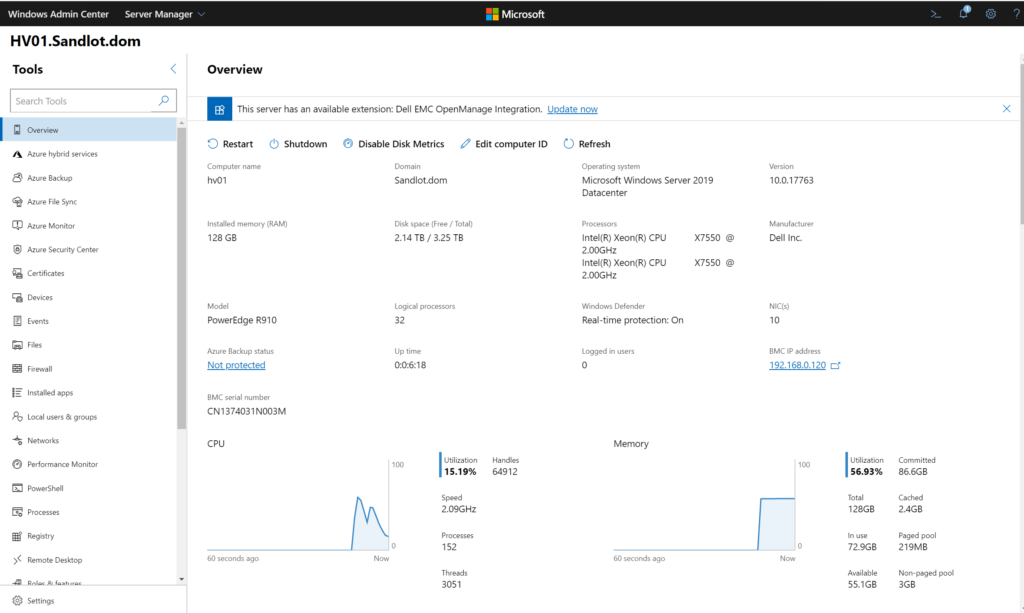
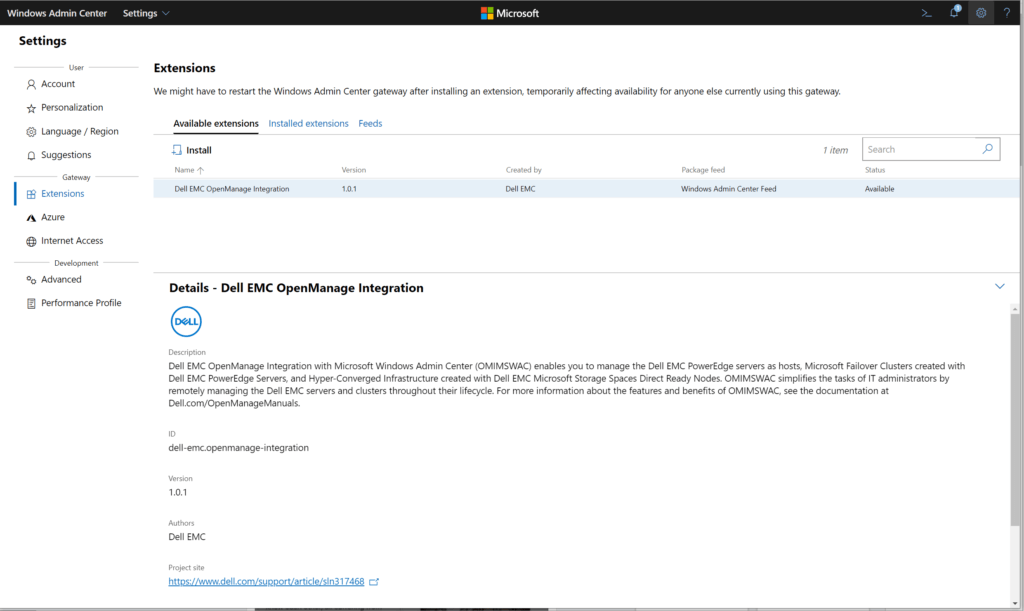
Once connected, in the Overview pane, you can see that Windows Admin Center automatically detected my Dell server and offered the OpenManage extension.
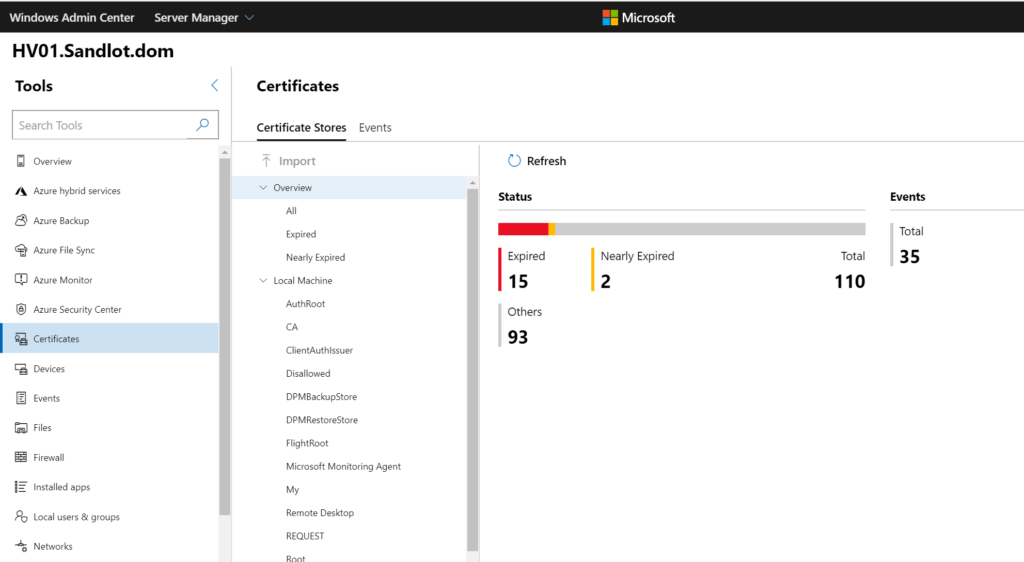
We can manage Certificates directly from WAC.
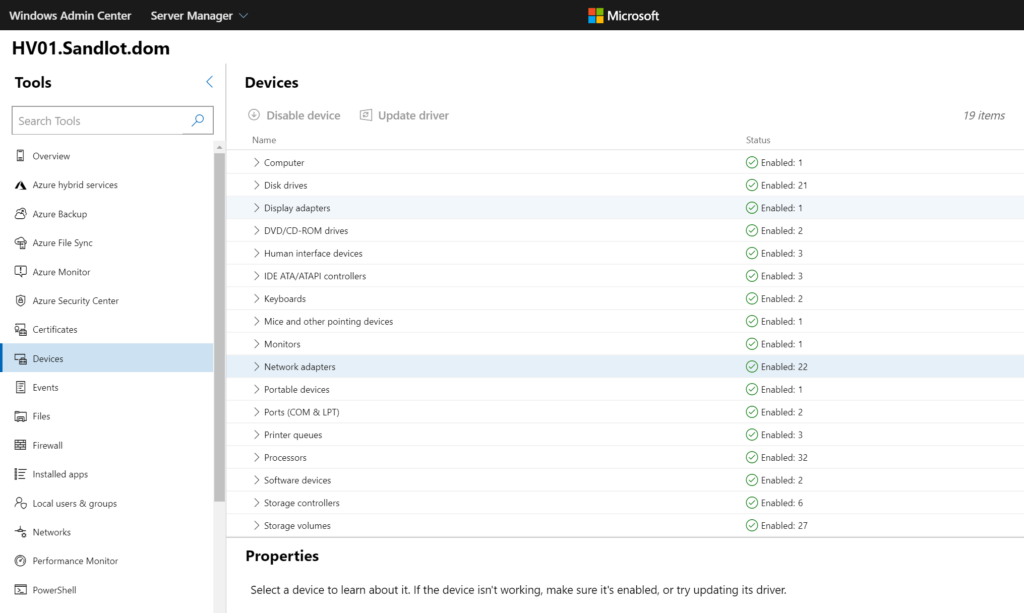
Under Devices, we can disable devices or update device drivers.
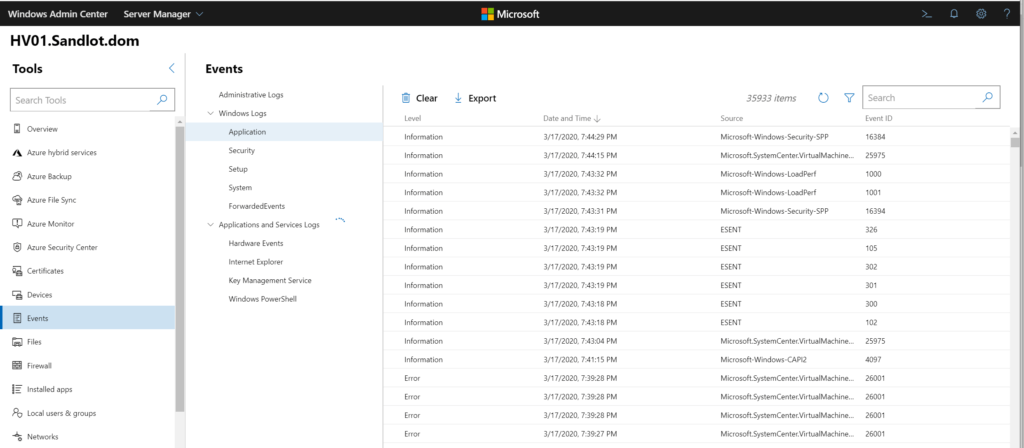
View and export Event Logs, if you’re not using my Azure Monitor Event Log Workbook with Log Analytics.
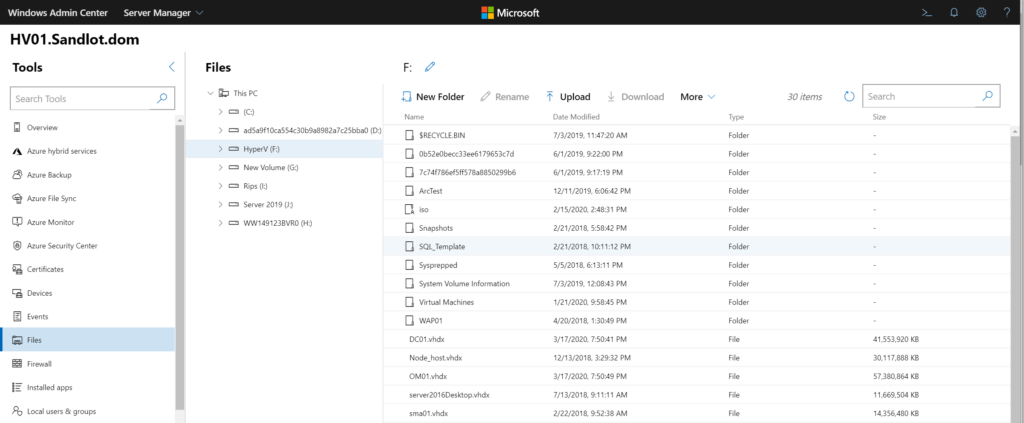
You can manage files and folders, upload and delete them as well.
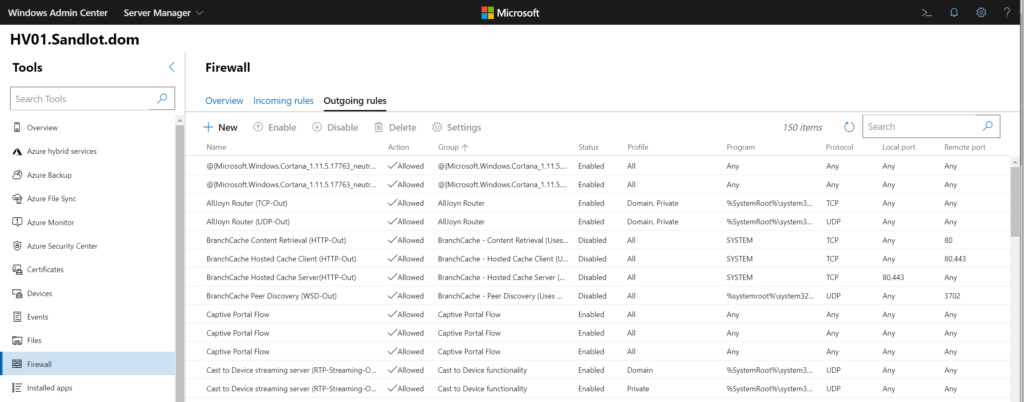
Under Firewall rules, we can modify incoming and outgoing rules.
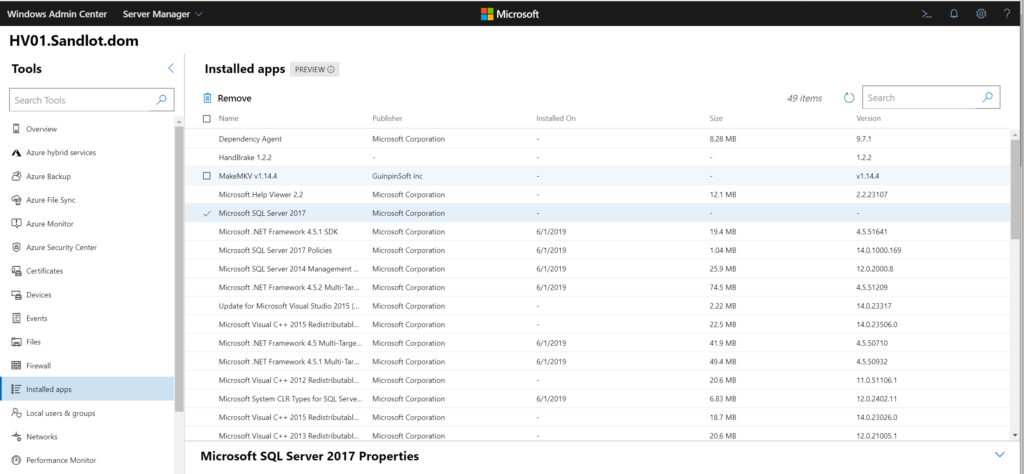
We can remove installed applications
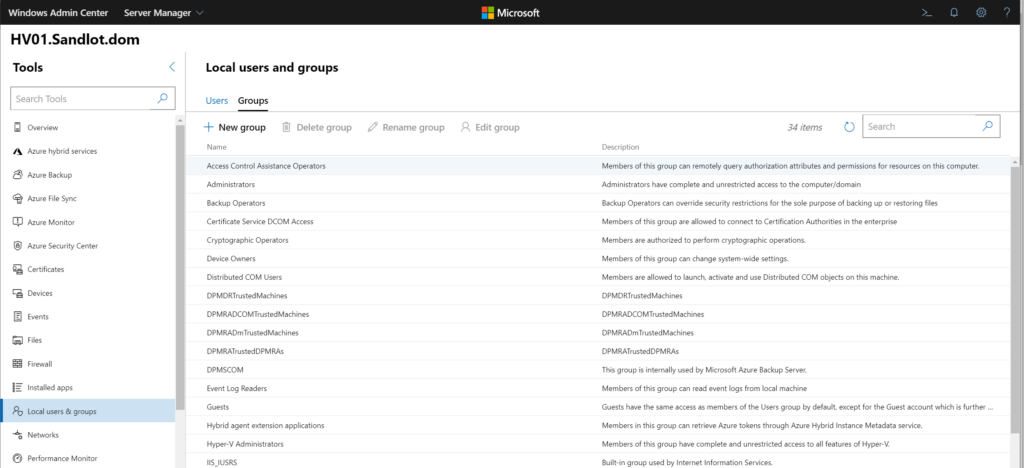
Modify users and groups for the server.
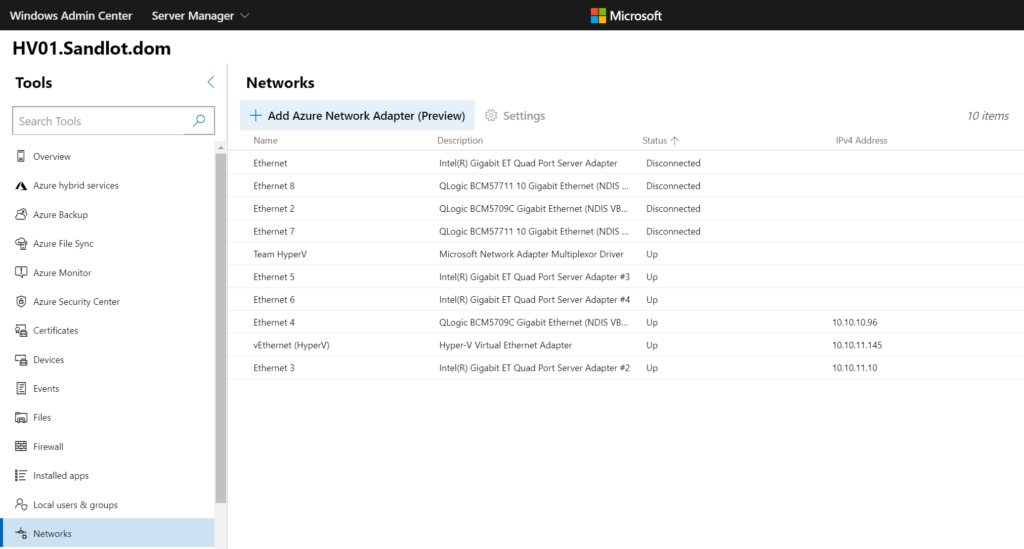
We can modify network adapter settings.
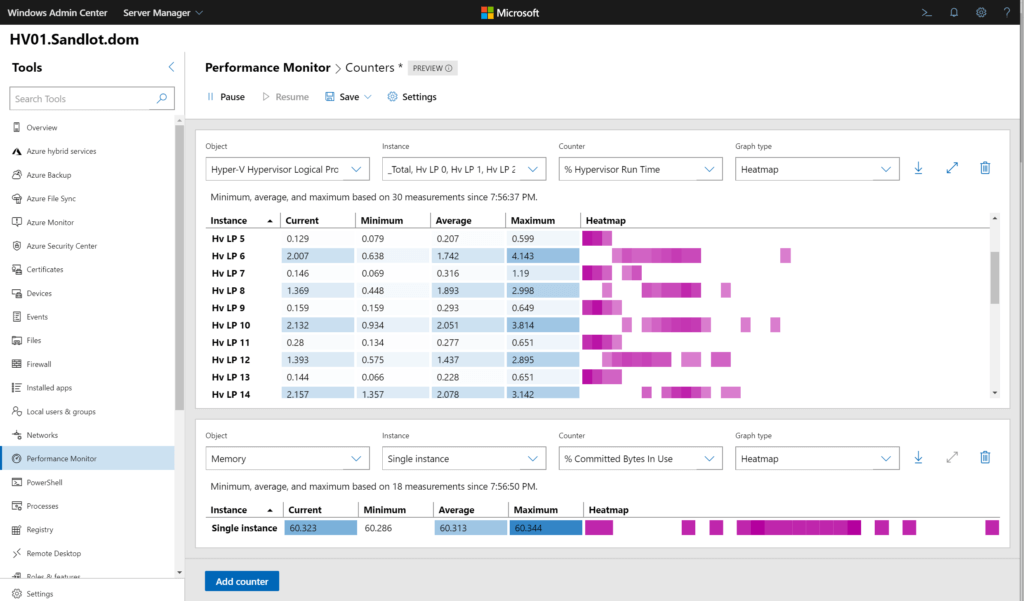
Performance Monitor can be run natively without being RDPed into the server. There are also a few different graph types and you can save the settings for later use.
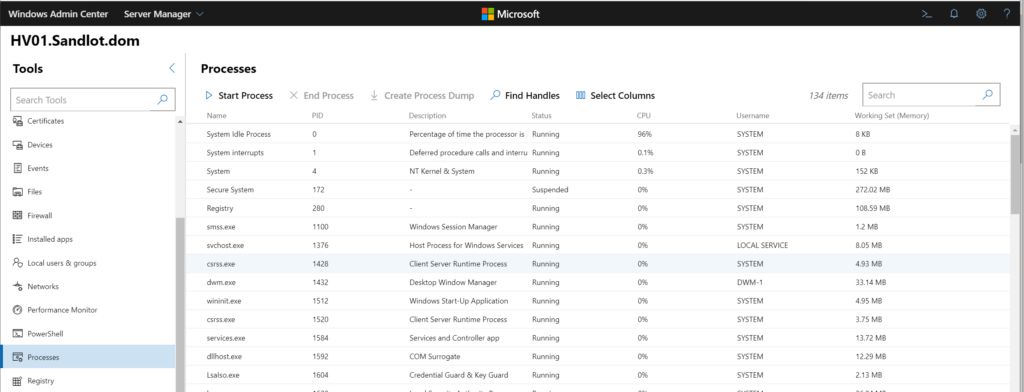
You can check processes.
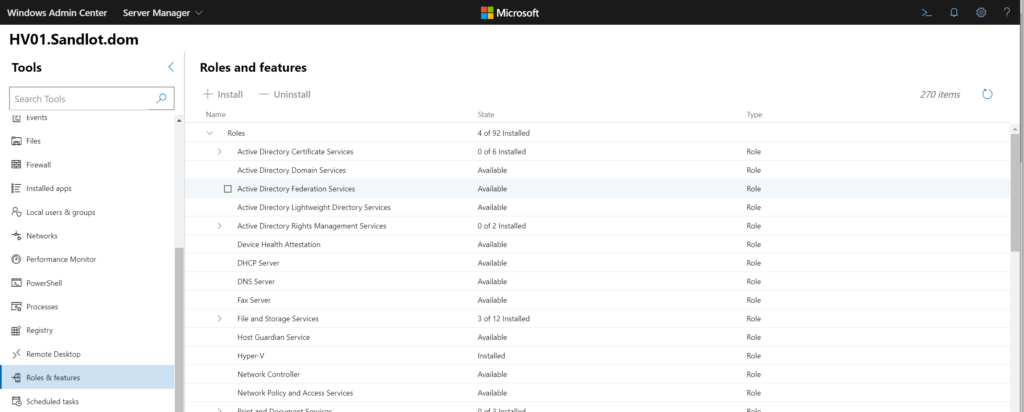
Roles and Features can be modified or installed directly from WAC.
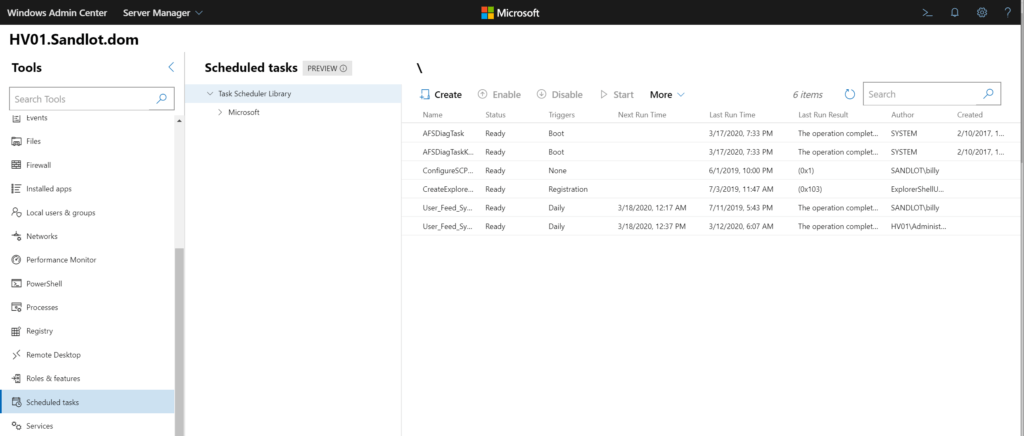
You can create, modify, or start scheduled tasks.
Finally you can run powershell remoting with a literal click of a button.
To recap on any old server we can:
- Modify Certificates
- Disable and update device drivers
- Look at event logs
- Modify files and folders
- Create, Delete or Modify firewall rules.
- Uninstall Applications
- Modify users and groups
- Run perfmon
- Modify network adapter settings
- Check running processes
- Modify scheduled tasks
- Modify roles and features
- Check services (not pictured)
- Modify the registry (not pictured)
- PowerShell remoting
And if all that isn’t good enough you can RDP into the server, even un-trusted ones.
Hyper-V and Clustering
But wait! There’s more. Yup. We can also manage Hyper-V and Clusters. When you add a cluster to Windows Admin Center it automatically discovers all nodes and adds them to the server management pane.
Within Hyper-V we get a summary of running, off, saved, paused machines with events and CPU and Memory.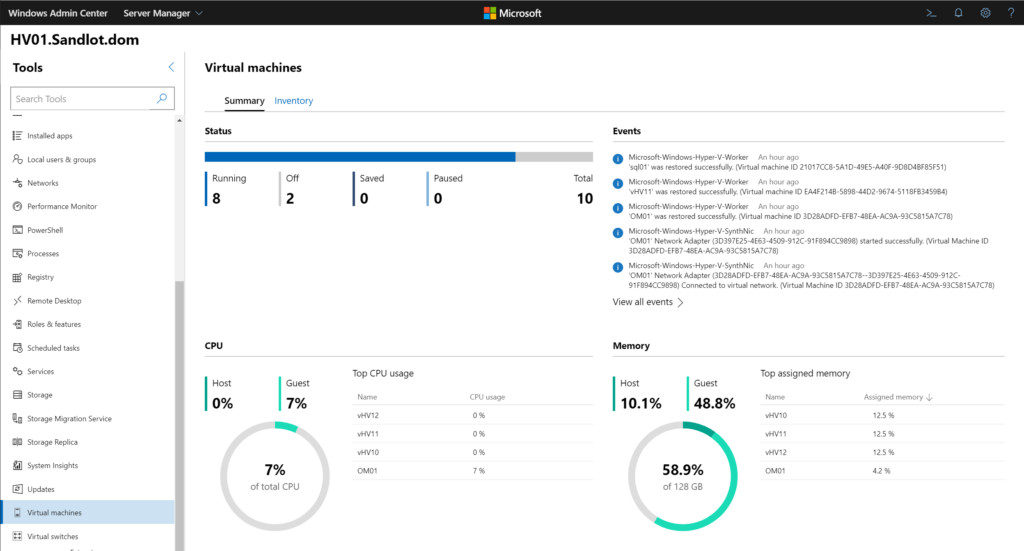
We can also create new VMs.
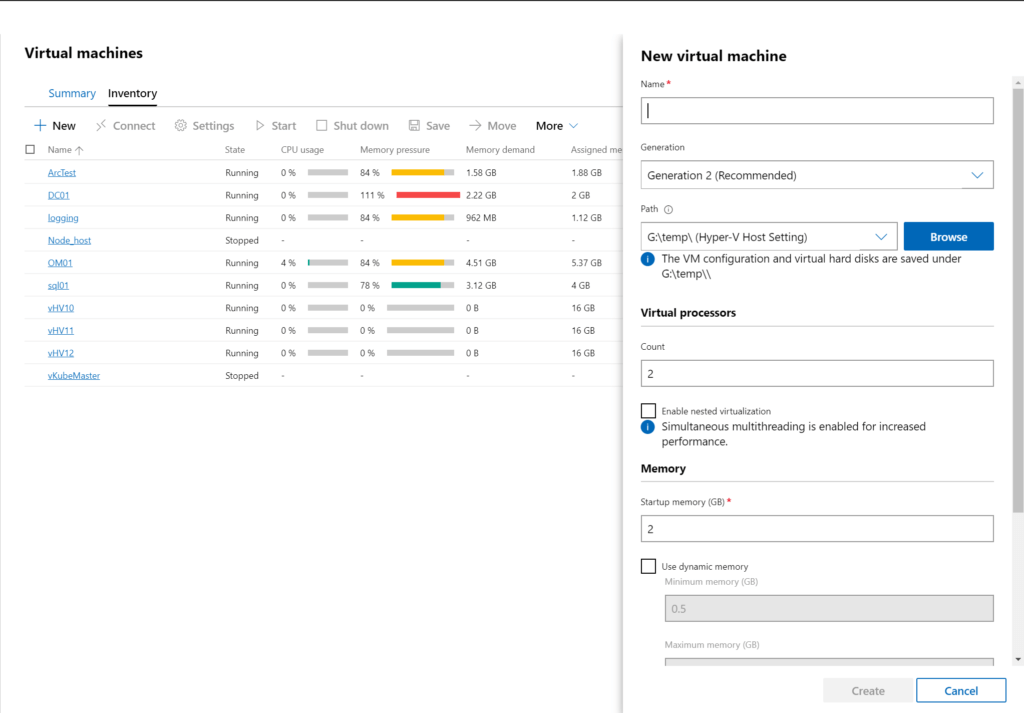
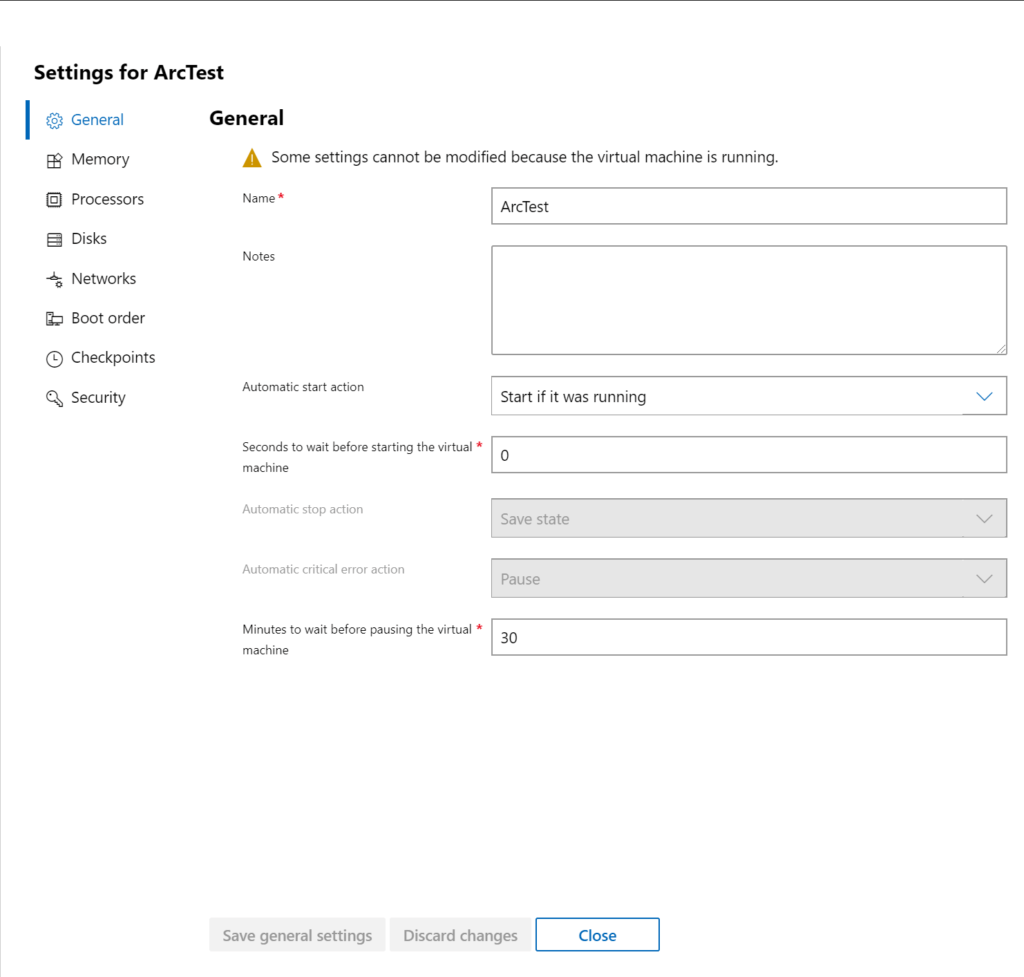
Modify settings of VMs. I also want to point out that little checkbox that says “enable nested virtualization” previously the only way to enable that was through PowerShell, now you can do it through GUI with Windows Admin Center.
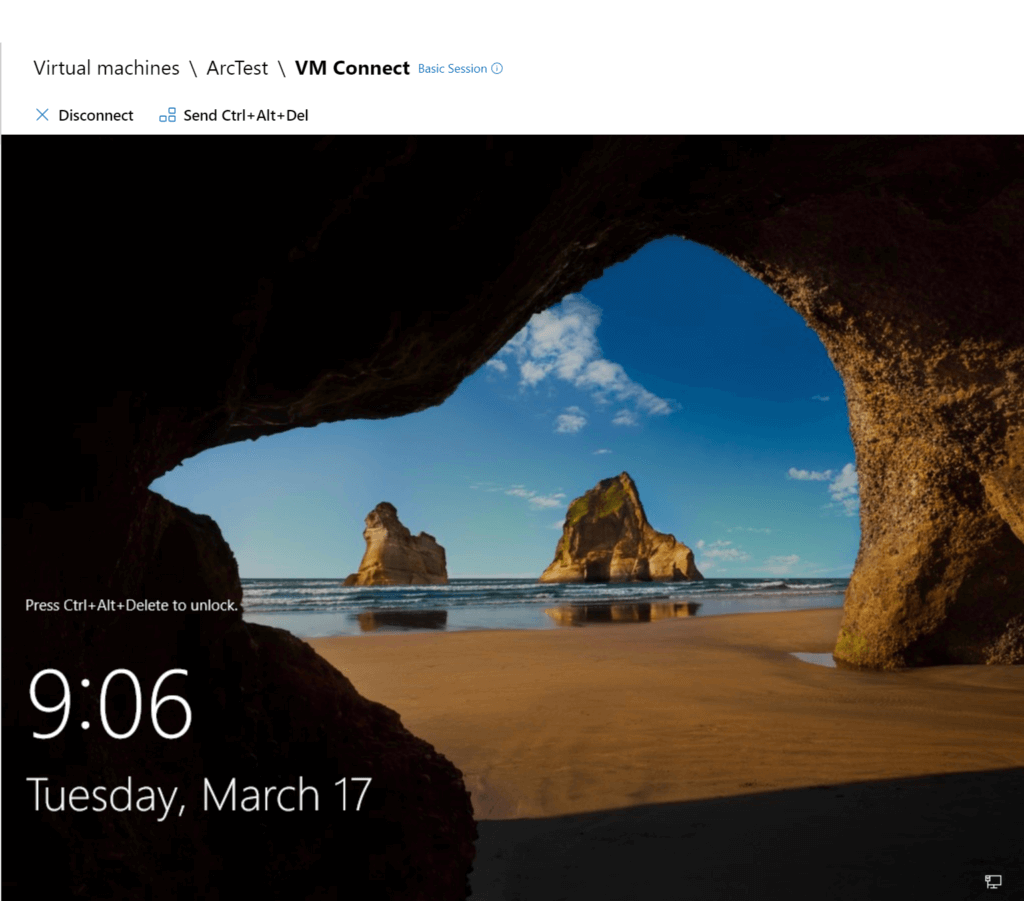
Even console in. Again note that I’m on my un-trusted laptop, connected to my HyperV server consoled into a domain controlled VM.
The overview of the VM gives you all the information you would expect like Host, uptime, dynamic memory enable, etc.
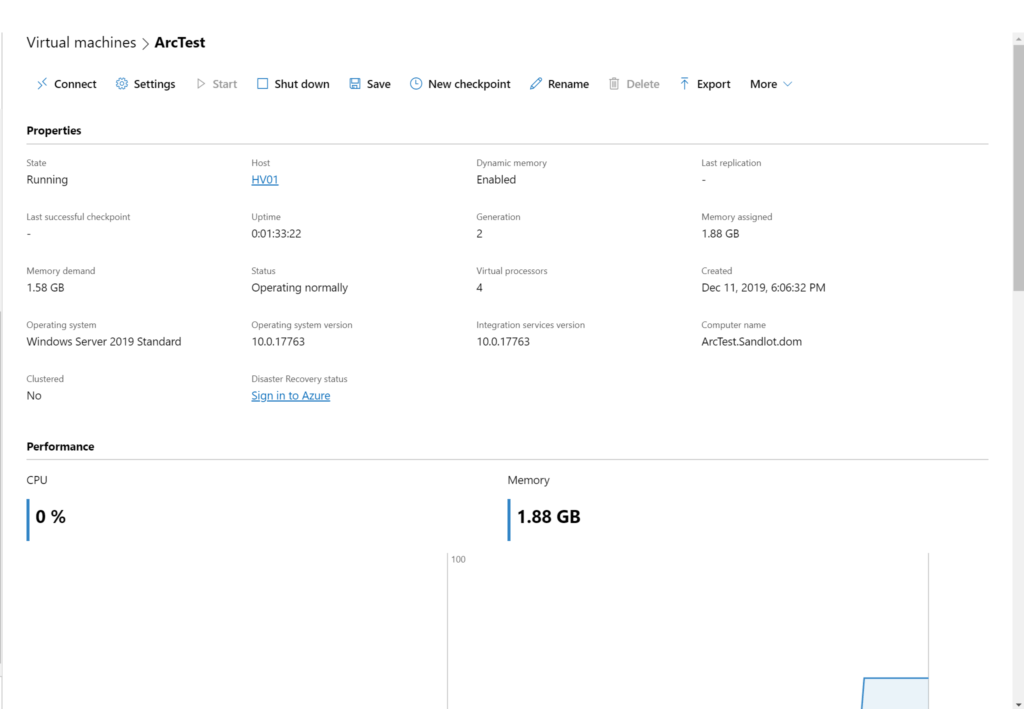
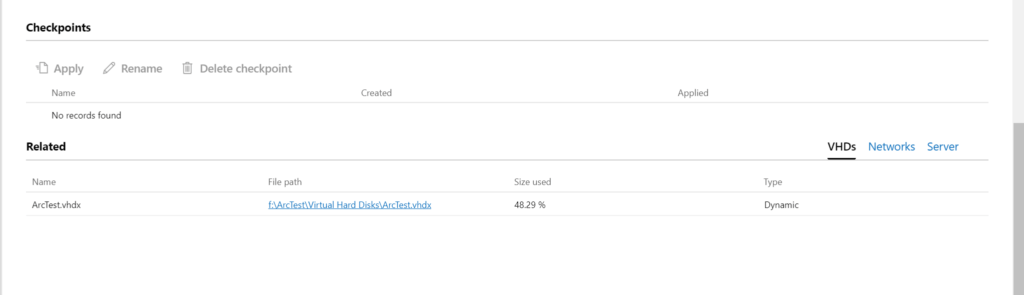
Below the performance section you get information on Checkpoints.
Active Directory, DCHP and DNS Extensions
There are also extensions to manage AD, DHCP and DNS.
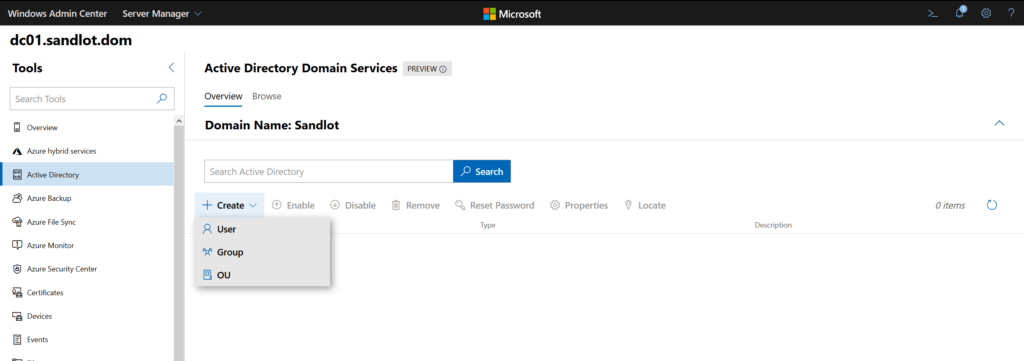
We can create Users, Groups and OUs.
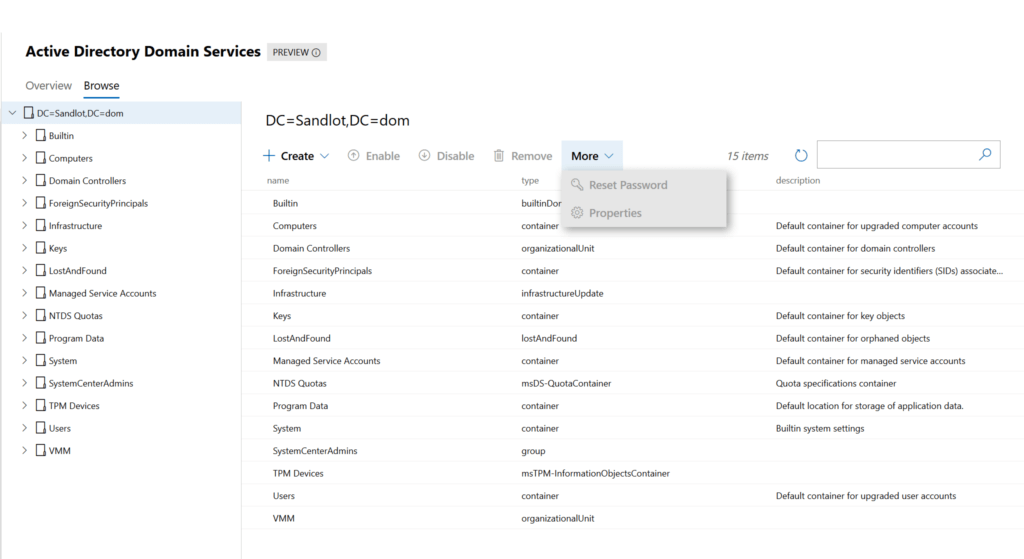
Reset passwords, enable and disable accounts.
Hybrid Cloud
There are a bunch of Azure related features. Microsoft’s focus mirrors my long held belief that the future is a Hybrid cloud. So they’ve included a number of Azure related extensions that you can use. I’ve used the ARC extension. Thomas Mauer has a number of posts on using Windows Admin Center with Azure. If you’re not in Azure yet, you can turn off the recommendations or even remove the extensions from what I’ve seen. Just know that they are there if you ever need them.
Summary
So in summary, we have a legacy tool that hasn’t been updated since 2014, with a major vulnerability that’s not going to get patched. And another tool that’s been updated 16 times in less than 2 years. One tool that all it does is RDP and another tool that’s literally primed to replace HyperV, Failover Clustering, ADUC, DNS, DHCP, MMC consoles. Allows you to remotely manage, Devices, Certificates, Networking adapters, Processes, Files and Folders, Users and Groups, Scheduled Tasks and a lot more. While also providing you one click PowerShell remoting and RDP if you really need it. Oh and that second tool is the primary focus for GUI improvements as outlined by the Principle PM of Windows Server.
Reading the comments that were anti Windows Admin Center the only conclusion I can come to was that they either haven’t used it, or only used it a year or more ago, or when it was still called Project Honolulu. Sometimes we have to change with the times, in my opinion this is a no-brainer multi benefit change. I would have loved such a tool when I was doing Sys Admin work. If I were still doing Sys Admin work the first thing I would do is install WAC in my environment.