In our Log Analytics workspace under the Azure Monitor umbrella, we have a number of predefined monitoring solutions. These are some of the ones I would consider to be a no-brainer installs in any Log Analytics workspace. The only reason really, to not install them would be if you’re simply not using the related product. The below listed are what I consider must install Azure Monitor solutions.
Part of the reason I consider them must install, is the value you get vs the cost to install them. Azure Activity Logs are free for 90 days with 90 days of storage, for instance. But lets look at how much logs each solution generates.
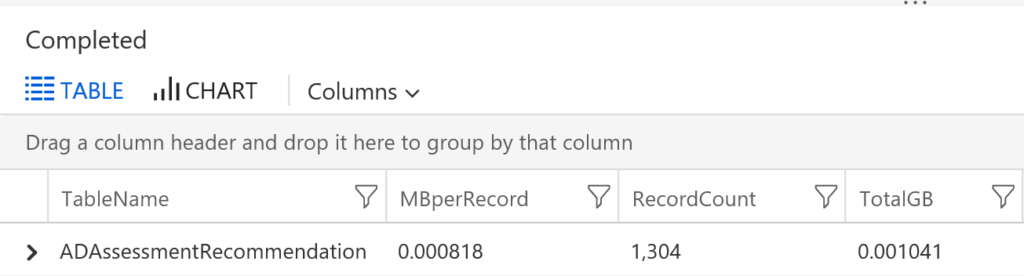
The Active Directory Assessment running every 7 days against 3 domain controllers, generated 1300 logs in the last 30 days.
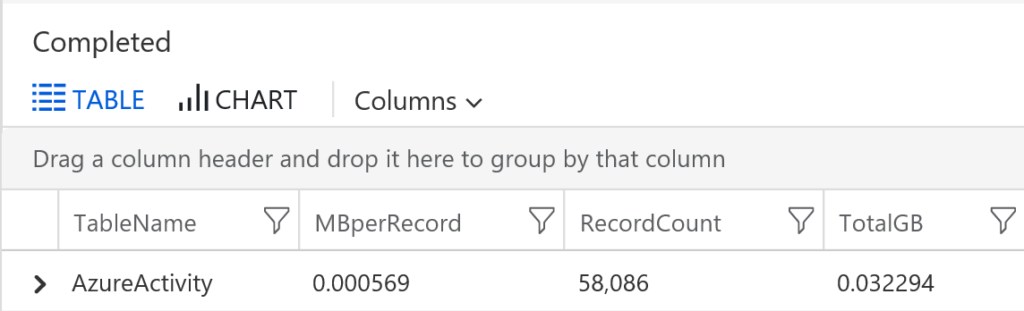
Azure Activity Logs in a good size production Azure environment generated almost 60k logs, but wasn’t even close to 1GB.
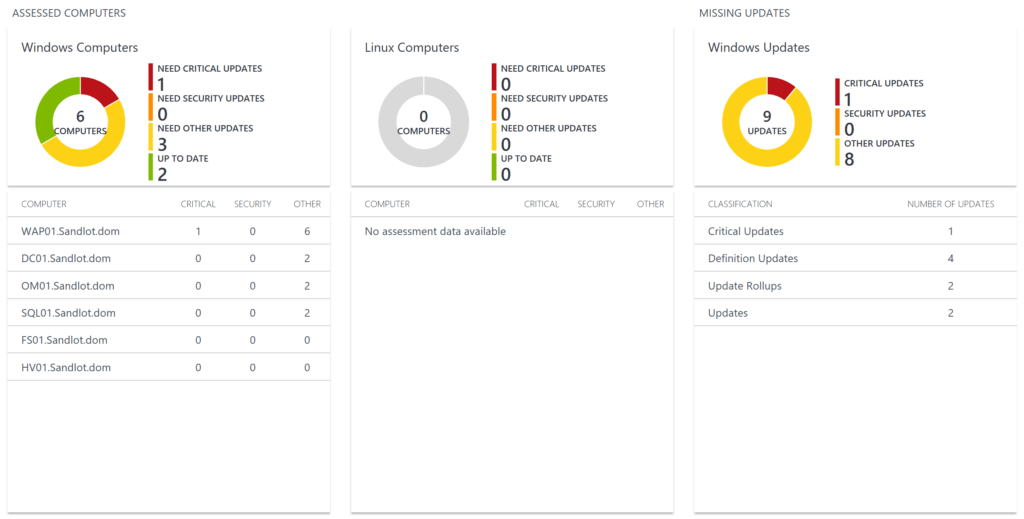
and finally data from my lab, with 2 SQL servers for the SQL Assessment (which runs ever 21 days), and roughly 6 servers reporting in the update data, and this is for the last 90 days. (one caveat here, Update and UpdateSummary tables have data in isBillable true and some in isBillable false, not sure why that is).
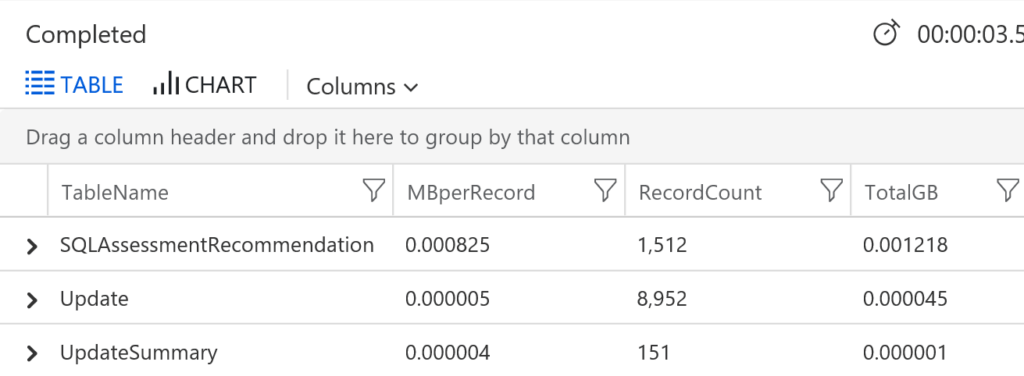
all told this data hasn’t even generated 1GB of data. Recall that log ingestion is billed at $2.30 per GB in Log Analytics. I think its well worth a few dollars a month to generate these assessments on your likely larger production environments.
Next I’ll show you a little bit of what you get with each solution.
Azure Activity Logs
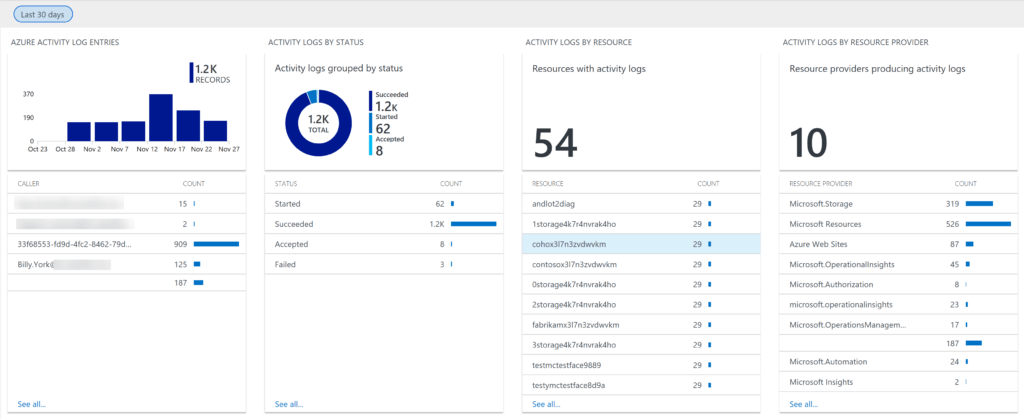
I would include the overview tile but its literally just the number of logs collected for that time period. Once you drill down is where you get more pertinent information. Names blurred to protect the guilty. (note this is from a smaller environment than the one above that had 60k records)
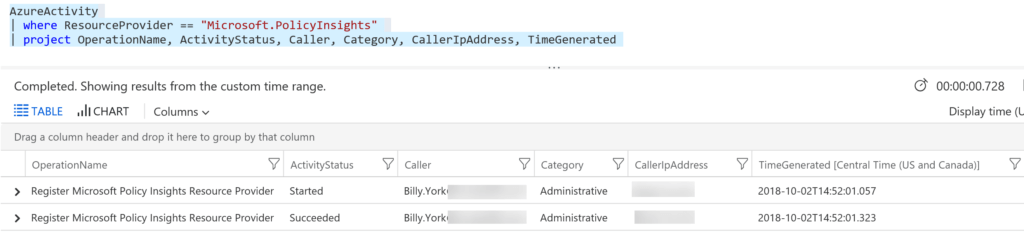
Of course you can log search. Here’s where I registered Azure Policy. You could have a lot of fun with this, like automation for evil Donnie Taylor does. Triggering alerts any time someone creates something. Or you could just use the logs like normal.
SQL Health Check
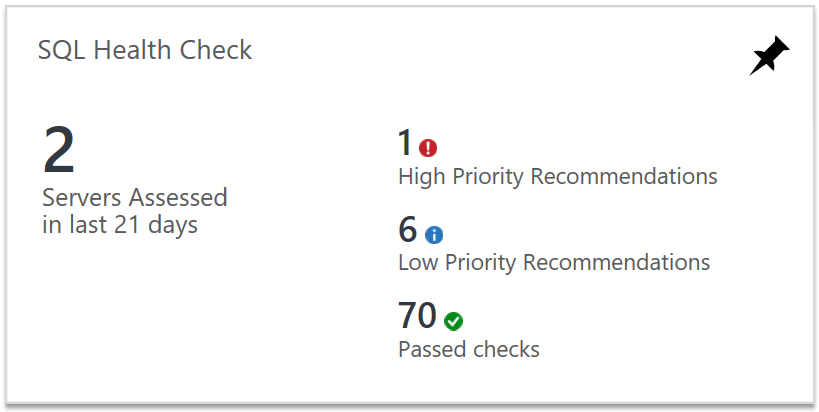
The SQL Health Check solution is one of my favorites and I’m not even a SQL guy. The overview tile is nice, giving you a summary of how many SQL servers were assessed, and a priority break down of the recommendations it found.
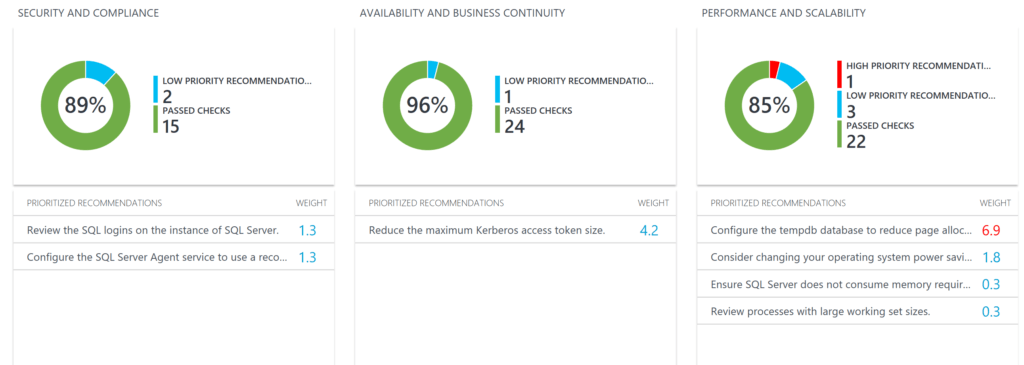
Once we drill down into the solution it shows us all the recommendations its assessing on. There are more to the right in this view that I did not include.
Selecting any of the tiles opens up a new window explaining each recommendation.
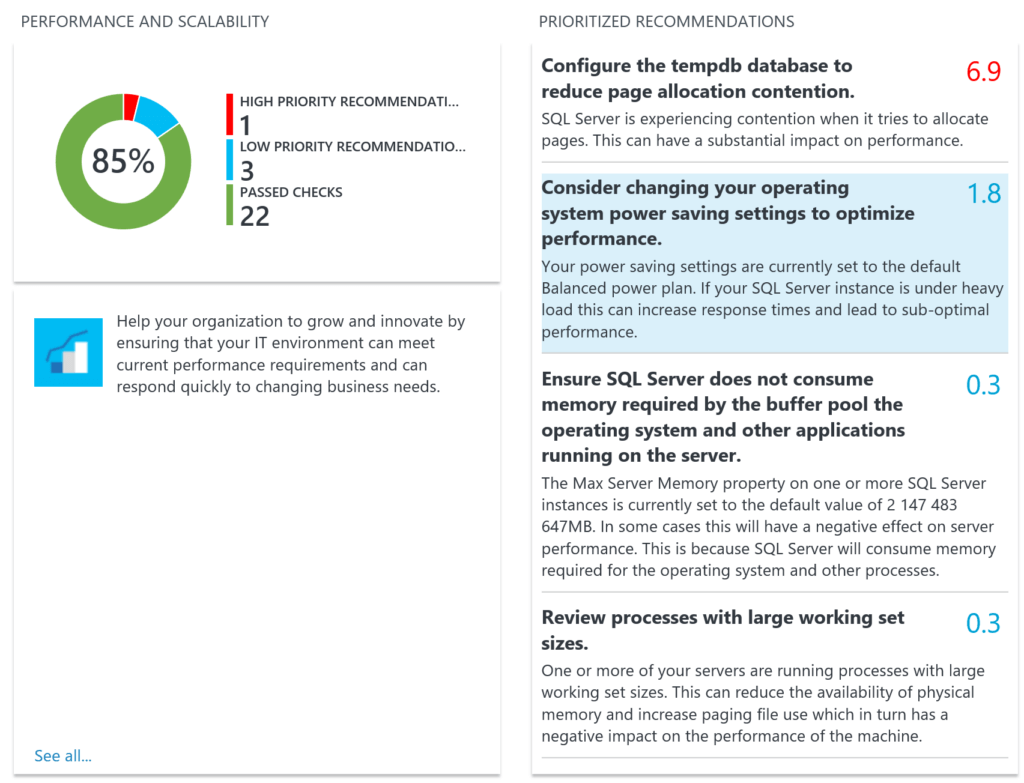
and then to the right of that it actually has suggested actions and how to remediate. For instance this one is about setting the Power Options. Apparently this is a known issue that MS could fix en mass but doesn’t want to potentially break millions of SQL environments.
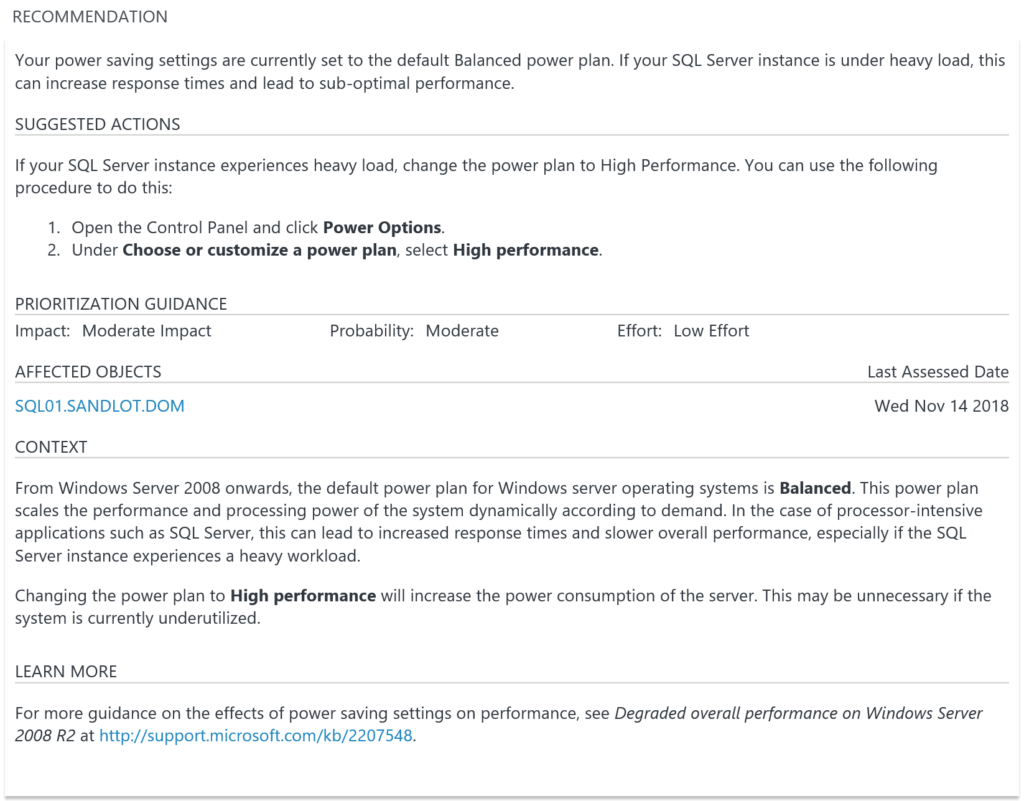
As you can see it has a number of recommendations. Unfortunately its just a health check that runs periodically. Currently there is no Microsoft provided SQL monitoring solution for you’re on prem SQL servers. I’m hoping they add one, because whoever did this one did a really nice job. With all the recommendations its likely you may not need some of the. You can ignore ones you don’t want, in the links I provided for the solutions there are outlines on how to ignore recommendations so they stop showing up in Log Analytics.
I’m not going to show the Active Directory solution because its almost exactly the same as the SQL one, just replace what its assessing in SQL with AD.
Update Management
Despite what the solution tells you when you deploy it, you don’t need the Azure Automation account to collect the logs. If you want to automate your windows updates thats what you need the Azure Automation account for. To just report on windows update status you can simply deploy the log collection portion of the solution.
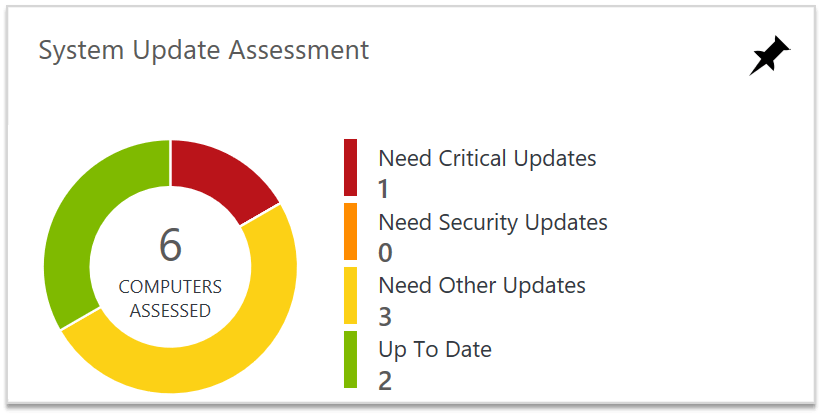
The overview tile gives us a nice donut clearly showing how many servers need critical, security or other updates.
Once we delve into the dashboard there are two Windows information tiles and two Linux ones. I wish this could be customized such that the Linux ones could be removed. If you don’t have any Linux machines in your environment, its just wasted space.
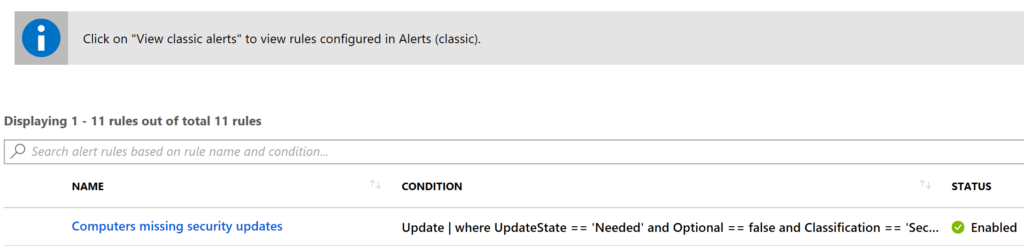
You also get an automatic Alert in your Azure Subscription. This thing will email you for every. single. computer. that needs updates, every day. That’s definitely one way to force people to update. On the other hand on, for organizations that update only one weekends or do testing in labs or development environments, a delay of sorts will need to be enabled.
These four solutions offer a lot of value for very little cost. This is why I put them in the must install if you’re using any of these products or services. Do you have any must install solutions for Azure Monitor?
2 thoughts on “Must Install Azure Monitor Solutions”
Comments are closed.