To monitor untrusted servers or to use a Gateway server in SCOM we need a certificate to successfully communicate with these servers. So, we need to create one specifically for this purpose. The certificate we will create in this blog works with both unstrusted servers not in a DMZ. As well as with SCOM Gateways which you would use if you needed to monitor servers in a DMZ or in another domain that has no trust to the domain that your SCOM Management servers are in. This certificate creation is using Active Directory 2012. The process may vary slightly for AD 2008.
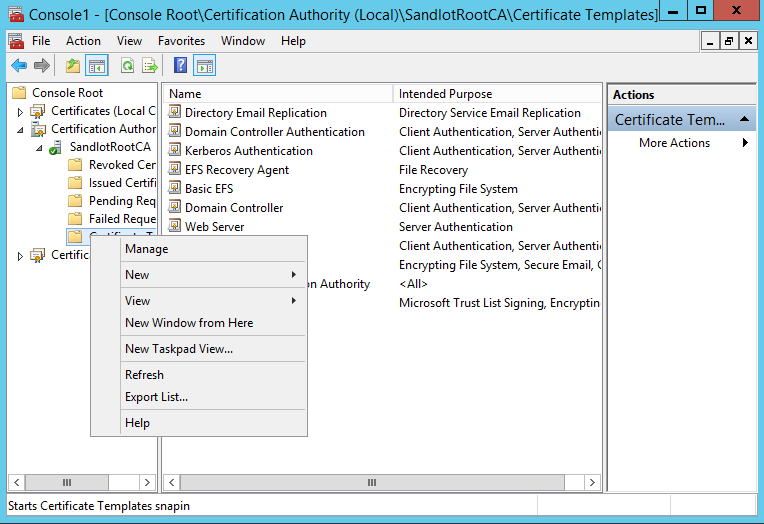
On your server hosting your Active Directory Certificate Services, open MMC and add the Certificate Authority snap-in. Right click on Certificate Templates and select Manage.
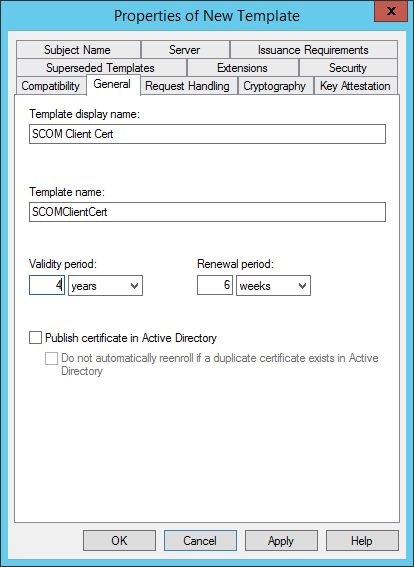
Find the Computer template, right click it and select Duplicate Template.
In the Properties of New Template on the Compatibility make sure Show Resulting changes is checked, Certification Authority is Windows Server 2003 and Certificate Recipient is Windows XP/Server 2003.
On the Request Handling tab, make sure Purpose is set to Signature and encryption and check Allow private keys to be exported.
On the Cryptography tab Check Microsoft Enhanced Cryptographic Provider 1.0 and Microsoft RSA SChannel Cryptographic Provider.
On the Security tab, give Authenticated Users Enroll.
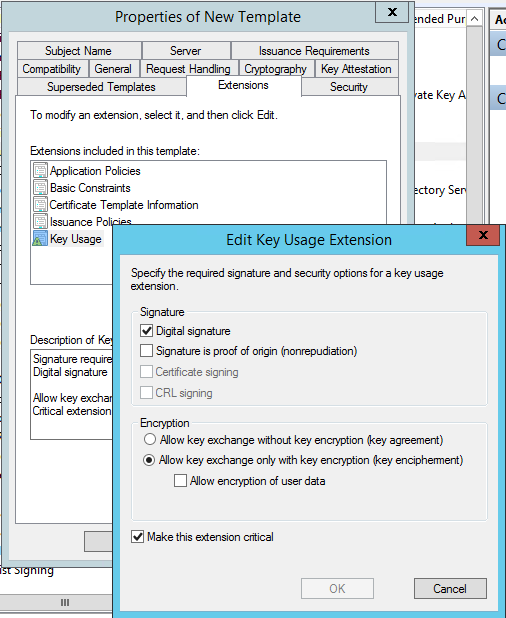
On Key Usage make sure Digital Signature is checked.
On the Subject Name tab, select Supply in the request.
Then select our newly created SCOM Client Cert.
Presumably, if you are going through this process, you want the template sooner rather than later. Well if you try to issue the certificate now, it will not be there. So open a command prompt as an administrator and do the following
gpupdate /force
and then
net stop certsvc
net start certsvc
Now if you open MMC and add certificates from any domain joined PC and request a new certificate, the certificate will be available. You can also find it from your CertSrv website at https://fqdn/certsrv if you have web enrollment enabled on your Active Directory Certificate Services