I was recently at a client who wanted to monitor a bunch of untrusted servers. These servers were not in their new Active Directory domain, many of them, were in fact not in any domain. And they were not in any DMZ, so the Management Servers could see them just fine. Thus no gateway(s) were required. This process is a pain, and during my deployment I followed several blogs, all of which weren’t entirely clear or skipped steps or didn’t include screenshots for vital parts. My intent is to be as thorough as possible, and include steps to verify what you are doing is working. I will also call out any steps if I skip or don’t provide a screenshot for them.
This is for monitoring untrusted servers without a Gateway Server, if you are looking for how to install at Gateway Server in SCOM my colleague Jim Moldenhaur has a nice blog post that works.
There are some prerequisites that we need before we begin this process.
- SCOM Specific certificate for enrollment of servers. See my previous post here to create the certificate.
- SCOM Management Server(s) must be able to resolve untrusted server(s) by name
- Untrusted servers must be able to resolve SCOM Management Server(s) by name
- Root CA certificate from AD Certificate Services must be imported on Untrusted servers
In this post we will setup our Management Server(s) to be able to add untrusted servers into the SCOM environment.
Overview of the Process covered in this post:
- Generate SCOM Client Certificate for Management Server.
- Import SCOM Client Certificate for Management Server with Momcertimport.exe.
- Restart Microsoft Monitoring Agent on Management Server.
- How to Confirm successful import.
Generate SCOM Client Certificate for Management Server and Import with Momcertimport.exe
So at this point you could go to https://fqdn/certsrv address of your Certificate Services server and get your certificate. However, it is much easier to get it through MMC. (this may not work in Server 2008, I have not tested it.)
So on a server that is joined to the domain, start MMC and click add, certificates. Expand the Personal Store, right click certificates, select All Tasks, select Request New Certificate.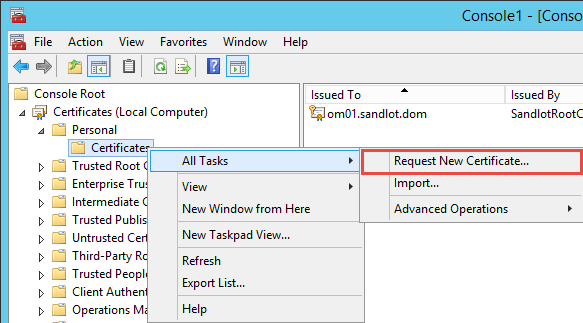
Click next, next and you should see your SCOM Certificate. Click the blue text under the certificate.
One the Subject of the Certificate Request change Subject Name to Common Name and Alternative Name to DNS. Type your FQDN of your SCOM Management server, in my case om01.sandlot.dom, add it to both Subject and Alternative name fields and click add for each.
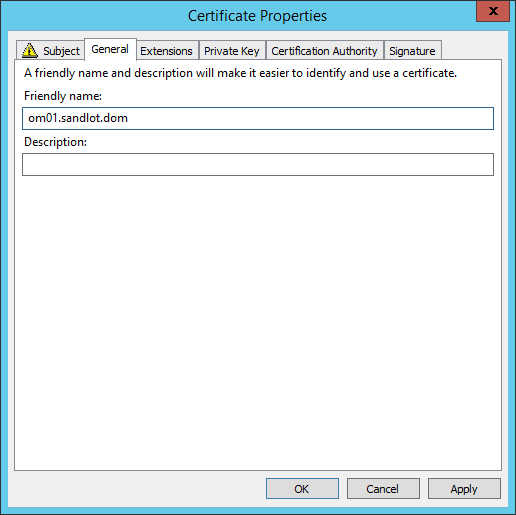
Under the General tab, add the FQDN of your SCOM Management Server to the friendly name field.
Click Apply and click OK. You should now not have any warnings for the Certificate Enrollment. Click Enroll.
You should see Succeeded.
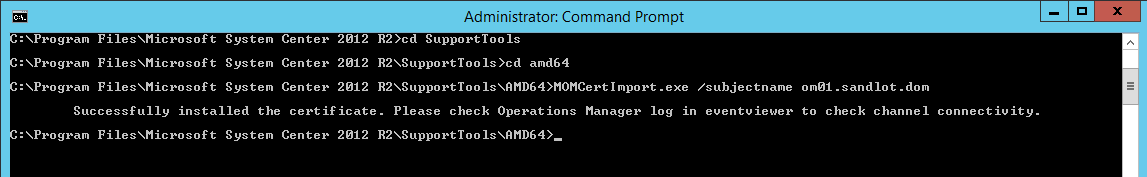
Now you need to use the Momcertimport.exe tool to import the certificate. The momcertimport.exe tool is on the SCOM ISO under the SupportTools folder. I usually just export the whole folder and put it with the Operations Manager install folder under Program Files. Note, you need to use the specific version of the momcertimport.exe for your OS, if your OS is 64 bit you need the .exe from under amd64 and the same applies for 32 bit OS.
Open a command prompt as an administrator and navigate to where you put the SupportTools. Type
momcertimport.exe /subjectname <FQDN of your management server>
Now open Services and restart the Microsoft Monitoring Agent Service.
There are a couple of ways to confirm that it imported successfully. In Regedit under
HKLMsoftwareMicrosoftMicrosoft Operations Manager3.0Machine Settings.
The ChannelCertificateSerialNumber will be reversed pairs of the Certificate in the MMC console. I have seen some certificates fail, so if you have a different number in here, simply delete the Registry key and try it again. I have even seen this fail with the same certificate that worked on the second try.
The other way to verify that the Certificate Imported successfully is to open Event Viewer, navigate to Operations Manager and look for event 20053 for the OpsMgr Connector, I believe the error is 20051 if it failed, but you’ll definitely see SCOM not happy if the import did not work.